Linux 7.0.6 is Out, and It Fully Patches the Dirty Frag Exploit
Dirty Frag has been the talk of the town (at least in Linux and open source circles) recently. The LPE was inadvertently exposed to the public, catching the Linux project and the various distros off guard.
Thankfully, a proper patch is now out, landing in Linux 7.0.6 and Linux 6.18.29 LTS. Fedora and Pop!_OS have already pushed their own fixes too.
What’s the fix?
The patch, authored by Hyunwoo Kim, the same researcher who found and disclosed Dirty Frag, addresses CVE-2026-43500, which now carries a CVSS score of 7.8 HIGH over on the National Vulnerability Database.
The root cause traces back to a 2019 commit that left two packet types unaccounted for in the rxrpc handling path, ones with pages fed in through splice() and ones with fragment chains attached.
The kernel did not treat either as shared memory, so it skipped making a safe copy and decrypted them in place. That left a window for a local attacker to reach in from userspace and tamper with those pages while decryption was happening, which is enough to get root.
The fix extends the existing check in two rxrpc functions to also catch those two cases, so they get copied to a private buffer before decryption like they should have been all along.
Linus Torvalds merged it on May 10, Linux 7.0.6 was out the following day, and the 6.18.29 LTS kernel got it too.
You can get the tarball for 7.0.6 over at kernel.org. This is intended for those who have the skill to install it manually, and if you are on an Ubuntu-based distro, we have a guide on how to do that.
Just keep in mind that this is a risky process to go through; only do so if you have backed up your data.
For Fedora and Pop!_OS users
Both distros had fixes out before 7.0.6 was officially released.
Fedora
Fedora kernel maintainer Justin Forbes announced earlier that the fix was already being pushed to the stable branch. Fedora 43 and Fedora 44 get it with the 7.0.4 kernel, and Fedora 42 users with 6.19.14-101.
Justin also says that they skipped an update to 7.0.5 for F43 and F44, as the fix was already implemented in their 7.0.4 builds.
To get it on my Fedora Workstation 43 setup, I first ran this command to get a list of any available updates:
sudo dnf update
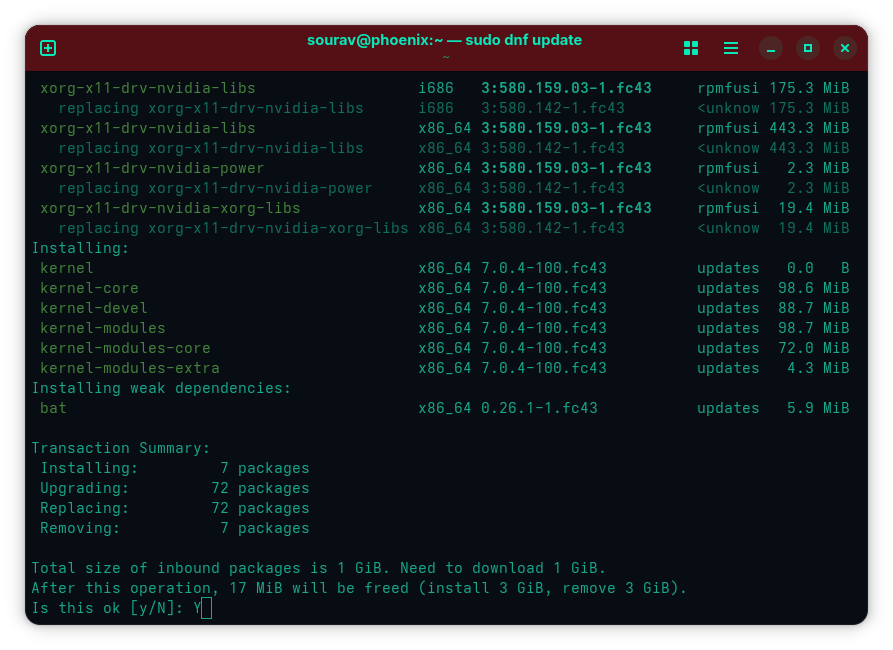
Getting the patched kernel on Fedora Workstation 43.
After verifying that I was getting the patched x86_64 7.0.4-100.fc43 kernel, I ran the following command to get the upgrade and pressed “Y” when prompted:
sudo dnf upgradePop!_OS
For people running the LTS releases of Pop!_OS, 22.04 and 24.04, System76 has released kernel updates covering both Dirty Frag CVEs. The esp4 and esp6 modules tied to the second CVE were patched and are said to be safe to re-enable.
For rxrpc, they went with disabling the module rather than patching it and are holding off on re-enabling it.
You can get the fixes by running:
sudo apt update && sudo apt upgradeRemember to reboot after the above is done running with:
sudo rebootFor further reading, our earlier Dirty Frag coverage has the full scoop on the exploit and the temporary workarounds from before the fix was available.
![]()
